
Large companies and small businesses are seeing an ever-growing number of cyber threats that attack their endpoints. Their regular endpoint security software may fail against advanced cyberattacks and render them ineffective and outdated. According to a report by Ponemon Institute, 2018 placed a destructive hit on 64% of organizations due to endpoint attacks. Read more

You have completed your annual phishing training. This includes teaching employees how to spot phishing emails. You’re feeling good about it. That is until about 5-6 months later. Your company suffers a costly ransomware infection due to a click on a phishing link.
You wonder why you seem to need to train on the same information every year. You still suffer from security incidents. The problem is that you’re not training your employees often enough.
People can’t change behaviors if training isn’t reinforced. They can also easily forget what they have learned after several months go by.
How often is often enough to improve your team’s cybersecurity awareness? It turns out that training every four months is the “sweet spot.” This is when you see more consistent results in your IT security.
Why Is Cybersecurity Awareness Training Every 4-Months Recommended?
Where does this four-month recommendation come from? There was a study presented at the USENIX SOUPS security conference recently. It looked at users’ ability to detect phishing emails versus training frequency. It looked at training on phishing awareness and IT security.
Employees took phishing identification tests at several different time increments:
- 4-months
- 6-months
- 8-months
- 10-months
- 12-months
The study found that scores were still good four months after their training. Employees were still able to accurately identify and avoid clicking on phishing emails. However, after 6-months, their scores started to get worse. Scores continued to decline as the months passed after their initial training.
To keep employees well prepared, they need training and refreshers on security awareness. This will help them to act as a positive agent in your cybersecurity strategy.
Tips on What & How to Train Employees to Develop a Cybersecure Culture
The gold standard for security awareness training is to develop a cybersecure culture. This is one where everyone is cognizant of the need to protect sensitive data as well as avoid phishing scams and keep passwords secured.
This is not the case in most organizations. According to the 2021 Sophos Threat Report, one of the biggest threats to network security is a lack of good security practices.
The report states the following:
“A lack of attention to one or more aspects of basic security hygiene has been found to be at the root cause of many of the most damaging attacks we've investigated.”
Well-trained employees significantly reduce a company’s risk. They reduce the chance of falling victim to any number of different online attacks. To be well-trained doesn’t mean you need to conduct a long day of cybersecurity training. It is better to mix up the delivery methods.
Here are some examples of engaging ways to train employees on cybersecurity. You can include these in your training plan:
- Self-service videos that get emailed once per month
- Team-based roundtable discussions
- Security “Tip of the Week” in company newsletters or messaging channels
- Training session given by an IT professional
- Simulated phishing tests
- Cybersecurity posters
- Celebrate Cybersecurity Awareness Month in October
When conducting training, phishing is a big topic to cover. However, it’s not the only one. Here are some important topics that you want to include in your mix of awareness training.
Phishing by Email, Text & Social Media
Email phishing is still the most prevalent form. SMS phishing (“smishing”) and phishing over social media are both growing. Employees must know what these look like so that they can avoid falling for these sinister scams.
Credential & Password Security
Many businesses have moved most of their data and processes to cloud-based platforms. This has led to a steep increase in credential theft because it’s the easiest way to breach SaaS cloud tools.
Credential theft is now the #1 cause of data breaches globally. This makes it a topic that is critical to address with your team. Discuss the need to keep passwords secure and the use of strong passwords. Also, help them learn tools like a business password manager.
Mobile Device Security
Mobile devices are now used for a large part of the workload in a typical office. They’re handy for reading and replying to an email from anywhere. Most companies will not even consider using software these days if it doesn’t have a great mobile app.
Review security needs for employee devices that access business data and apps such as securing the phone with a passcode and keeping it properly updated.
Data Security
Data privacy regulations are something else that has been rising over the years. Most companies have more than one data privacy regulation requiring compliance.
Train employees on proper data handling and security procedures. This reduces the risk that you will fall victim to a data leak or breach that can end up in a costly compliance penalty.
Need Help Keeping Your Team Trained on Cybersecurity?
Take training off your plate and train your team with cybersecurity professionals. We can help you with an engaging cybersecurity awareness training program that helps your team change their behaviors to improve cyber hygiene. You can reach us at (860) 577-8060 or use our convenient contact form.
Insider Threats have been on the rise lately and companies find it hard to figure out the best security service or strategy that will thwart them. According to research, incidents associated with insider attacks had a 44% rise in the last two years. Employees contribute to about 40% of these threats with easy access to sensitive information. Business owners must deal with such incidents by wielding weapons as strong as those used against external attackers. Read more

One of the big draws of a laptop computer is that you can use it anywhere. You don’t need to have it plugged in all of the time because it has an internal battery.
Your laptop may start out with several hours of battery life when you first buy it. However, the lifespan can get shorter as time goes by and battery health takes a hit. Sometimes this can be due to a lack of PC maintenance. Other times, it's due to the environments that the laptop is subject to (such as a hot car).
Seeing your laptop’s battery capacity shrink can be frustrating. There are several things that you can do to increase the time you can go without needing to plug it in.
Lower the Display Brightness
The brighter your display means the more battery power it’s taking. Have you ever hit the automated low battery mode on a laptop? Then you know you immediately notice a difference in brightness. This is because that setting turns down the brightness. It's one of the ways to reduce battery consumption.
You can turn down the brightness of your screen in your display settings. You can also use the brightness keys that are usually in the top row of keys on a laptop keyboard.
Reduce PC Battery Use in Power/Sleep Settings
Here is one way to increase the time that you can use your unplugged laptop without a power source. Adjust some of its power and sleep settings.
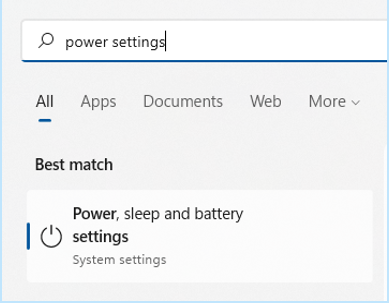
If you’re using Windows, open the search on the Task Bar. Type in “power settings." This directs you to the power, sleep and battery settings in your system settings.
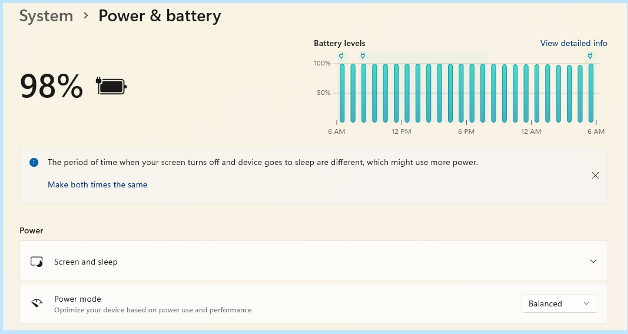
Look for any tips at the top for increasing battery longevity. This includes making the time your screen goes dark after inactivity and the time it goes to sleep the same.
Then review the settings (such as Screen, Sleep and Power mode). Find the ones that will reduce your PC’s battery consumption. This will extend the time that you can go without a new charge.
Enable Battery-Saver Mode
You don’t need to wait until your PC hits 10% for it to go into battery-saver mode. You can control this and enable it yourself in your system settings.
Do you know you’re going to be without a power source for a while? Put your PC in power-saver or battery-saver mode right away so that you can extend the charge as long as possible.
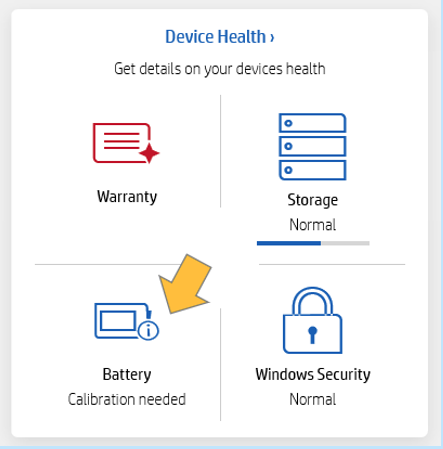
Use the Manufacturer’s Calibration Tool
Manufacturers will have their own PC maintenance tools installed that you can use for battery calibration. Sometimes calibrating the battery can correct an issue with a battery life. This is especially true if life has gotten shorter than when you first purchased your laptop.
Look for a manufacturer’s built-in maintenance app. It will usually be on the Task Bar unless you have hidden it. When you open that, you may find that you need to do a calibration or other maintenance task.
Get a Computer Tune-up
If you have processes running in the background, it can sap your battery life. Processes that aren't needed can often run anyhow. Getting a computer tune-up from your IT provider can solve a lot of different issues. This includes computers that get sluggish and battery life.
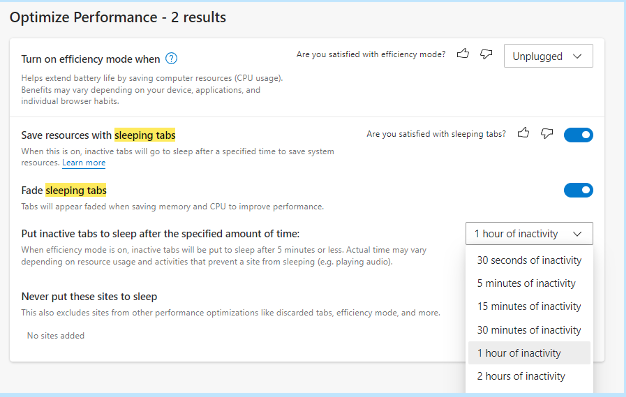
Consider Using Microsoft Edge Browser for Its Efficiency Settings
If you keep a lot of browser tabs open while you’re working on your PC. They could be sapping your battery power.
Consider trying Microsoft’s Edge browser. It has been gaining in popularity ever since it incorporated the Chromium engine. This is same one Chrome uses.
The browser has several power-saving features that you can enable in your settings. Search “sleeping tabs” in Edge settings to find these. They include:
- Enable efficiency mode (choose from the available options).
- Enable Sleeping Tabs and fade them when asleep.
- Choose when you would like to put inactive browser tabs to sleep to conserve power.
Turn Off Unnecessary Apps Hogging Power
Check the apps that are running on your PC in the Task Manager. Do you really need them all to run when you’re unplugged and trying to conserve battery power?
Often processes that aren’t 100% necessary all the time will be running. These include an update service or cloud storage syncing app. Close the apps that you don’t need to use at that time to lengthen battery life.
Keep Your PC Out of Too Much Heat or Freezing Temps
Both excess heat and freezing temperatures can be bad for a computer. This includes shortening the battery life.
You should never leave your laptop in a car on a hot day or when it’s freezing outside. Also, it might not seem particularly hot to you but if it’s sunny the inside of a vehicle can heat up pretty quickly. Be aware of the temperature extremes that your laptop is subject to.
Looking for a PC Tune-Up or Battery Replacement?
We can help you with a full system tune-up or a laptop battery replacement if needed. Don’t struggle when you can have that fixed in no time! Give us a call today at (860) 577-8060 or fill out our contact form and let’s chat.

The security of IT services has been reduced over the years. This is due to traditional authentication methods like usernames and passwords. While this has been considered the best security strategy for decades, the increased susceptibility to cyber-attacks means it is time to switch lanes. Passwordless authentication is one of the go-to security options in recent times. According to research in 2021, it has positively impacted the security of many companies in the U.S. and Canada. Why is it creating such a buzz?Read more

Credential theft is now at an all-time high and is responsible for more data breaches than any other type of attack.
With data and business processes now largely cloud-based, a user’s password is the quickest and easiest way to conduct many different types of dangerous activities.
Being logged in as a user (especially if they have admin privileges) can allow a criminal to send out phishing emails from your company account to your staff and customers. The hacker can also infect your cloud data with ransomware and demand thousands of dollars to give it back.
How do you protect your online accounts, data and business operations? One of the best ways is with multi-factor authentication (MFA).
It provides a significant barrier to cybercriminals even if they have a legitimate user credential to log in. This is because they most likely will not have access to the device that receives the MFA code required to complete the authentication process.
WHAT ARE THE THREE MAIN METHODS OF MFA?
When you implement multi-factor authentication at your business, it’s important to compare the three main methods of MFA and not just assume all methods are the same. There are key differences that make some more secure than others and some more convenient.
Let’s take a look at what these three methods are:
SMS-BASED
The form of MFA that people are most familiar with is SMS-based. This one uses text messaging to authenticate the user.
The user will typically enter their mobile number when setting up MFA. Whenever they log into their account, they will receive a text message with a time-sensitive code that must be entered.
ON-DEVICE PROMPT IN AN APP
Another type of multi-factor authentication will use a special app to push through the code. The user still generates the MFA code at login. Rather than receiving the code via SMS, it’s received through the app.
This is usually done via a push notification and it can be used with a mobile app or desktop app in many cases.
SECURITY KEY
The third key method of MFA involves using a separate security key that you can insert into a PC or mobile device to authenticate the login. The key itself is purchased at the time the MFA solution is set up and will be the thing that receives the authentication code and implements it automatically.
The MFA security key is typically smaller than a traditional thumb drive and must be carried by the user to authenticate when they log into a system.
Now, let’s look at the differences between these three methods.
MOST CONVENIENT FORM OF MFA?
Users can often feel that MFA is slowing them down. This can be worse if they need to learn a new app or try to remember a tiny security key. What if they lose that key?
This user inconvenience can cause companies to leave their cloud accounts less protected by not using multi-factor authentication.
If you face user pushback and are looking for the most convenient form of MFA, it would be the SMS-based MFA.
Most people are already used to getting text messages on their phones so there is no new interface to learn and no app to install.
MOST SECURE FORM OF MFA?
If your company handles sensitive data in a cloud platform, such as your online accounting solution, then it may be in your best interest to go for security.
The most secure form of MFA is the security key.
The security key, being a separate device altogether, won’t leave your accounts unprotected in the event of a mobile phone being lost or stolen. Both the SMS-based and app-based versions would leave your accounts at risk in this scenario.
The SMS-based is actually the least secure because there is malware out there now that can clone a SIM card which would allow a hacker to get those MFA text messages.
A Google study looked at the effectiveness of these three methods of MFA at blocking three different types of attacks. The security key was the most secure overall.
Percentage of attacks blocked:
- SMS-based: between 76 - 100%
- On-device app prompt: between 90 - 100%
- Security key: 100% for all three attack types
WHAT IS IN BETWEEN?
So, where does the app with an on-device prompt fit in? Right in between the other two MFA methods.
Using an MFA application that delivers the code via push notification is more secure than the SMS-based MFA. It’s also more convenient than needing to carry around a separate security key that could quickly become lost or misplaced.
LOOKING FOR HELP SETTING UP MFA AT YOUR COMPANY?
Multi-factor authentication is a “must-have” solution in today’s threat climate. We would be happy to discuss your barrier points and come up with a solution together to keep your cloud environment better secured.
You can reach us at (860) 577-8060 or via our contact form.

A hybrid office setup is a procedure in which a firm’s executives and employees work on-site and remotely. The idea is to offer workers and managers the best of both worlds.Read more
How much does your business rely on technology to keep your organization running forward? As business technology becomes more complex, it’s becoming increasingly popular for organizations to have their own internal IT departments to manage and maintain it. Yet, small businesses don’t often have the necessary funds for such a feat. How can your company afford quality IT service? You can start by pursuing managed IT solutions from a managed service provider.
Read more



